Today’s article covers a topic of recent interest KRACK.
Many of you, may have already read some articles about it, if you like me follow the blogs and technical information sites.
To be honest with the first articles that i found, i did not understand much.
This is because, a few days ago we started talking about KRACK, without knowing exactly what it was specifically.
It was only known that a research group at the University of Leuven in Belgium had discovered a system to “pierce” the famous WPA2 wireless protocol.
For those who do not know what is the WPA2, know that in 99% of cases in which you will connect to a wireless network, when you enter the password to access the network, the selected protocol is the WPA2.
So no one is safe, no one will be saved from the informatic holocaust, or maybe not?
First we see where the problem is.
KRACK WPA2 – What is it?
Before seeing what precautions to take to solve the problem, we understand what is.
KRACK stands for Key Reinstallation AttaCK that is the ability to force the WPA2 protocol to re-install the key used to encrypt the connection.
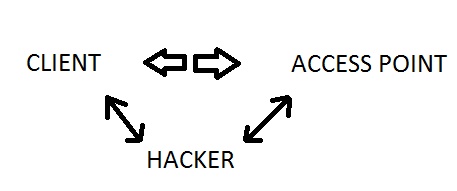
For the more experienced, it is a variant of the classic known cracking method man-in-the-middle.
The hacker who wants to get to know your data is placed in the middle of the communication between you and your Access Point.
All the packages that travel in this connection are captured by the software installed on the hacker device, which starts sending specially modified packages, by extending it to the correct interlocutor.
So far, there is nothing new and who will chew a bit of computer security, will know that this possibility exists.
For this reason there are well-designed protocols and that base their security on advanced encryption mechanisms.
In the case of WPA2, the protocol uses a 4-way handshake system.
The client, to start the connection to a WiFi network, exchanges packets, useful to confirm that it and the access point share the same key and create a new encryption key that will be used throughout the connection.
Installing the new encryption key takes place at the third step of the protocol.
This is where the flaw discovered in WPA2 comes into play.
WPA2, also provides for the possibility of losing packages during its phases.
If the third message is lost, the access point will send the package again.
The client received this package will re-install the certificate, and the counter will start from zero again.
The problem is right here.
This process allows the hacker to send the same message multiple times to the client and using injection and decoding techniques, will be able to decode the packets slowly.
In the worst case, you may even be able to force the installation of a fake key that knows very well and by that time will be able to decrypt the packets without any difficulty.
The problem would not exist if the key installation occurred only once, unfortunately this is not the case.
KRACK WPA2 – Devices Involved
The devices involved in this WPA2 flaw are all modern wireless devices.
No operating system or wireless device is immune to the problem.
Windows, iOS, Android, Mac, Linux, WiFi router etc.
Contrary to what you might think the worst attacks can be brought against devices with Android and Linux.
This is because both Linux and Android use the open version of WPA2 called wpa_supplicant.
This type of attack, with this version of the protocol, allows the hacker to replace the installed key with a fake zeros.
Instead, it does not happen with Windows and other systems that use proprietary protocol versions, but they are not completely immune because they are still open to more complex attacks.
KRACK WPA2 – Possible dangers
The reason that the computing environment is in turmoil these days is very simple.
Such a flaw is not a small matter.
If KRACK was put to work, a hacker would be able to steal your username and password, card numbers and sensitive data, or inject malicious code in apparently healthy sites.
As you will understand, if this were to happen, then it would be a real computer holocaust.
KRACK WPA2 – Solutions
Fortunately, the situation is risky but not critical.
The reason is very simple.
The attack to be put in place must meet several requirements:
- Client device with WPA2 flawed
- Access Point with WPA2 Failed
- Hacker who is remote to wireless, that is very close to your home (who does not have a hacker as a neighbor)
Moreover, even if the attack is successful, it is said that the hacker is able to steal your data.
This is because more and more communications take place via HTTPS protocol, which adds an additional level of communication encryption.
So after opening the first door, the hacker would find another door to open and it is not said that he can.
In this case, it depends very much on the app you are using or the site visited.
If properly using HTTPS, he cannot steal any data.
Instead, if it is not configured properly and parts of the communication is not protected, the attacker might be able to steal that information.
Anyway, back to the three points seen before, to solve the problem you need to eliminate one of those three elements.
So the advices are:
- Upgrade your device. Windows and other systems have already released a patch to fix this problem. Android should do it soon.
- Upgrade your routers and modems. Not all manufacturers are ready or willing to patch in the short term, some say the problem is limited and will only release the patch if some cases are found.
- With this point i want to point out that this attack can not occur if i connect to the network by cable or i am connecting to my wireless in my remote mountain hut. So my advice is “Do not access wireless that you do not know if you have not already updated your device.”
One last thing, when I first read some topic about KRACK, the first thing I thought was to enable access control via MAC address on my router.
Well this is completely useless, because this type of attack does not access your network, or even after the attack has been successful, you will also be able to modify MAC address data.
KRACK WPA2 -Insights
If you are interested in further information about KRACK, i recommend you visit the site created specifically of the discoverers of the flaw: krackattacks.com
If you prefer to see an example of attack, watch this video.
KRACK WPA2 – Conclusions
The press has given much emphasis to this news, because, on the contrary, the problem is not to be underestimated.
As you have seen, the different patches for different devices will soon be available.
The problem lies in understanding who should install them.
For client devices, it is very likely that the operating system will be upgraded as in the case of Windows.
I doubt that old devices are the same rule.
For example, Windows 98 is no longer supported by the updates, so forget the automatic update.
Not only that, many users often disable automatic updates because they consider them intrusive.
Perhaps one day every six months they dedicate it to this purpose, but in the meantime they remain uncovered.
Finally, who will update the devices as a modem or router?
In this case you may need to manually download the update and apply it.
Not everyone is able to accomplish a task like that.
It is not even said that the manufacturer has released the patch, because he believes the problem is limited.
Do you explain to them that long-range knots are always in the comb and that, even if limited, is always a problem?
If the article has been useful to you or found interesting, remember to share it with your friends and if you want to stay up to date on the latest news, subscribe to my pages and the YouTube channel.
Andrea